Why Reusing an Email Password can be Very Costly
Passwords are a tricky beast. It is nearly impossible not to have tens and hundreds of local and online accounts requiring passwords. We use passwords to:
- Log into devices
- Log into communication and software portals
- Order physical and digital assets online
- Send secure documents to banks and tax preparers
- Log into online applications and services
Most websites will no longer allow you to order something from them without creating an account if you do not already have one. While these accounts provide benefits to you as a customer, such as order history and tracking, it also means one more set of account credentials to manage. Over time, user ID and password credentials have become a nearly unmanageable byproduct of using the internet.
In response, people often employ shortcuts to help them remember account credentials. This may be reusing credentials, creating easy to remember passwords, or using dates and names they are not likely to forget. And who can blame them? Anyone would struggle to remember 100's of unique user id and password combinations and their corresponding sites. Unfortunately, reusing passwords introduces a tremendous amount of risk to your data and privacy. This post covers one of the worst passwords to reuse: your email password.
Why Reusing an Email Password can be Very Costly
When it comes to password credentials, there are some things you can do to help protect yourself. They are:
- Using password manager software to track all account credentials. This means you only have to remember the credentials to that software and your credentials are encrypted so nobody else can access them.
- Using different combinations of user IDs and passwords. This reduces the number of accounts at risk if an account is ever hacked. Keep in mind, companies can also get hacked at no fault of your own. When they do, anywhere those credentials were duplicated is now also at risk.
- Creating hard to hack passwords. This means not using numbers that relate to things in your life like phone numbers, addresses, the year you were married, your child's birthday, etc. Also, the lengthier the password, the longer it should take to crack that password. Adding in capitalization and special characters will also increase the difficulty.
In addition to these precautions, there is one type of account whose credentials should never be reused for other accounts. It is important to do everything you can to protect this account from ever being hacked. The account you least want to get hacked is:
Your email account!
The importance of protecting email account credentials is often overlooked when compared to bank accounts and other accounts where credit cards are stored. However, email accounts are the single most important account you never want to lose control over. This is because our email accounts are what we use as credentials for all of our online accounts including banking. There are 3 main reasons the credentials for an email account should never be reused.
First, if someone else gains unauthorized access to your email account, they can send emails to others, such as your contacts or people you have previously corresponded with, pretending to be you. Emails of this sort often include viruses, links to places that will install some sort of malware on their systems, or a page asking for their credentials so their attack can spread.
Gaining access to our contact lists, and being able to pose as us, are reasons why these types of attacks spread so quickly. When people receive emails from someone they know and trust, there is a much higher likelihood they will open the email. If an email gets hacked and you still have access, send a message to your contacts with a subject line telling them not to open emails from you until further notice. It is also wise to call or message those whose information you have.
Second, having access to your email allows someone else to see what companies you do business with. All they have to do is browse through your inbox, subfolders and deleted items for those received from different companies. Whether they are offers, order confirmations, shipping confirmations, newsletters or something else, these emails often confirm you have an account with that company.
Once someone knows what companies you have already created accounts with, they can use the access to your email account to change the passwords on those accounts. With access to your email, they can trigger a password reset for any accounts they choose. Using the email sent to your hacked account, they can click the reset link and set the password to whatever they want. As long as they have access to your email account, they can attempt a password reset for any account you have that uses that email as the user ID.
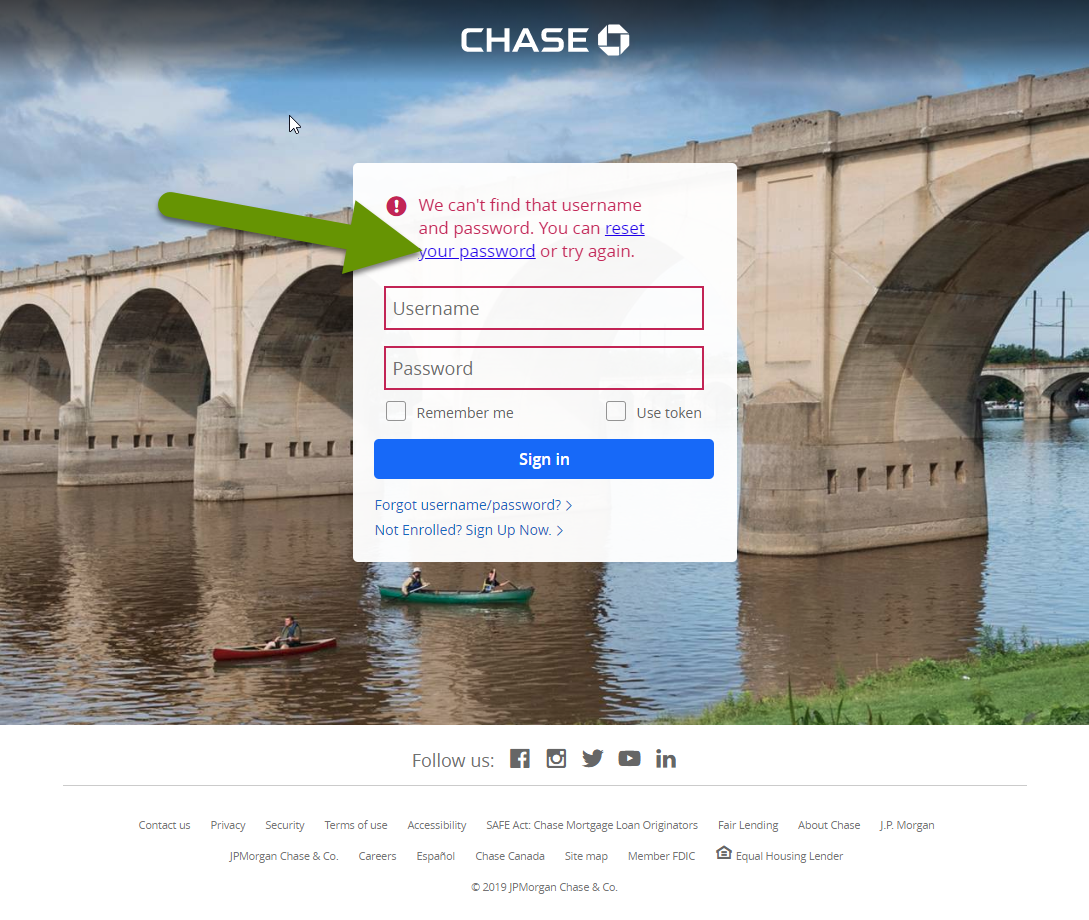
Third, if the password is reset for any account, including the email account originally hacked, you have lost control for this account. This often means you are locked out without access of any kind. So, not only is the integrity of your files at risk, confidentiality is lost, and the files are not available to you. NOTE: When this happens, it can take weeks, months or longer, to regain control of any account. Recovery often depends upon the account provider's service and your follow up.
It is always frustrating to have a set of credentials compromised, regardless of the type of account. However, losing control over some accounts is far more detrimental than others. Email accounts are especially dangerous accounts to lose access to because they are used to access all sorts of other accounts. With access to your email, someone can send emails posing as you, reset other account passwords and lock you out of your own accounts. This is why it is especially important not to reuse the credentials used with email accounts.
As always, knowing the best way to protect yourself, and which are most important to protect, is the first step in maintaining data privacy and confidentiality.

