Technology Round Up: Office 365 Outage, Apple Settlement & More
Keeping up with all the news about technology would be a full time job. From new applications to Ransomware attacks to security breaches, there are an unlimited number of sub-categories within technology to focus on. Even if you were diligently tracking technology news, there could be some recent items you may have missed.
This post covers some recent technology events you may not be aware of, but could benefit from knowing.
Technology Round Up: Office 365 Outage, Apple Settlement & More
Office 365 Outage
You may have noticed that Office 365, (O365), was offline on Tuesday evening for nearly 4 hours. Luckily, users with locally installed applications could use them just as they would anytime they were offline or not connected to the internet.

However, there were plenty of things users could not do during the outage. Anyone using the online version of O365 applications, which requires internet access, would not have been able to use those applications even with internet access because they were unavailable. Also, the following abilities were unavailable:
- Adding new users
- Modifying or deleting existing users
- Changing account preferences
- Managing licenses including purchasing additional licenses
- Exporting a user's mailbox
- Resetting a user's password
- Using the Teams communication application
- Accessing files stored in OneDrive
- Sychronizing file changes in Teams, OneDrive and SharePoint
The takeaway: Outages of this size are uncommon for Office 365. Smaller, maintenance-style windows of downtime are more common. Still, this is a good reminder that applications running in the cloud introduce the potential risk of losing access if it goes down or internet is unavailable. Using an online version of applications is fine for many users. However, if you have a business or tight deadlines, you should install applications locally.
Apple Class Action Settlement
A current class action lawsuit with Apple has reached a settlement. This lawsuit may affect you if you have ever owned an iPhone. The lawsuit, Shamrell, et al. v Apple Inc., addresses issues with the following versions of iPhones:
- iPhone 4
- iPhone 4S
- iPhone 5
According to the settlement website, California citizens who purchased one or more iPhone 4, 4S or 5 smartphones from Apple or a third-party retailer whose sleep/wake power button stopped working or only worked intermittently within 3 years of the purchase, may be entitled to as much as $24 per device.
NOTE: Anyone whose device was already repaired or replaced by Apple for free due to a non-working sleep/wake button is automatically excluded from this settlement.
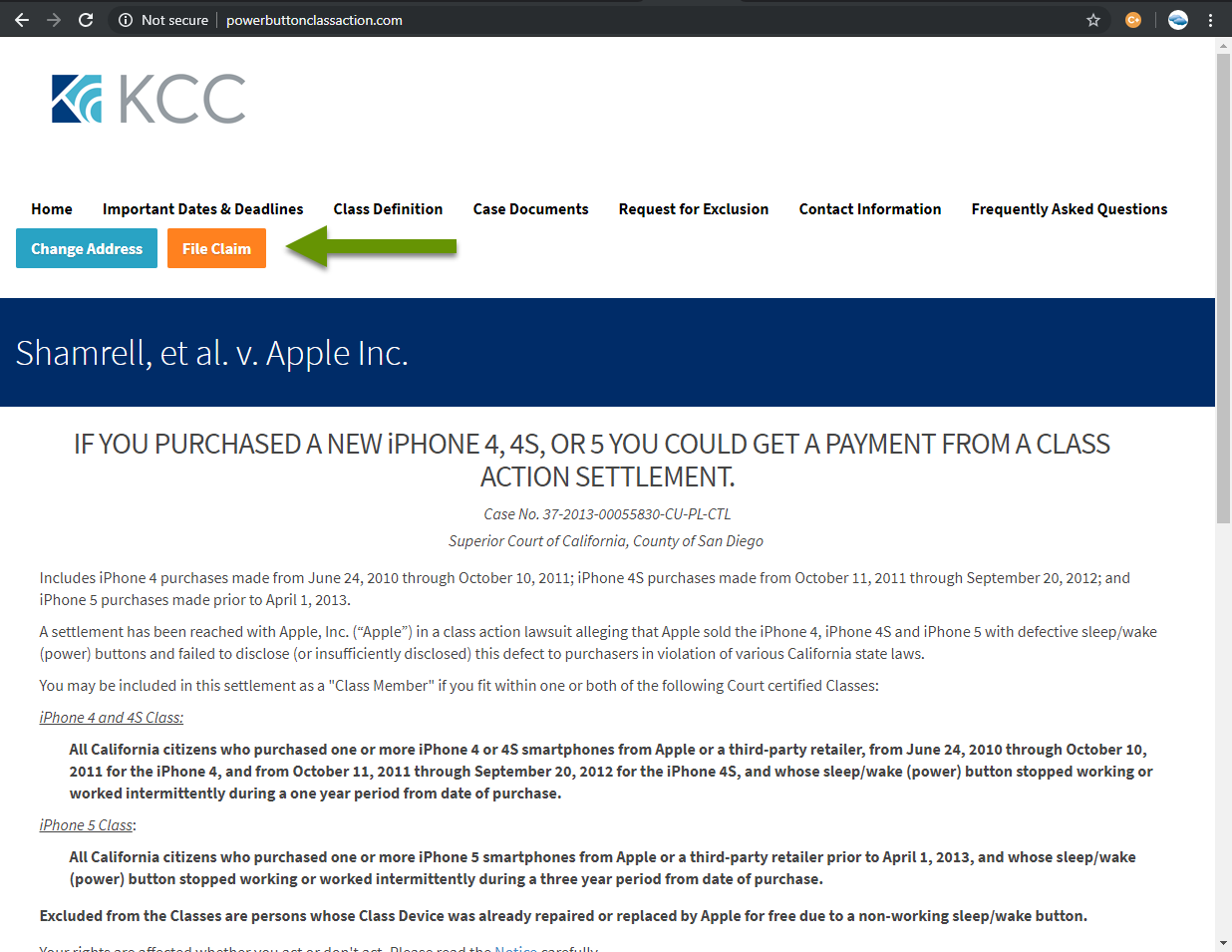
If you have ever purchased one of these model phones during the specified time periods, you may receive an email with a claim number as part of the class action suit. However, even if you do not receive a claim number, you can visit the site and file a claim. Simply click the "File Claim" button at the top of the website and submit the number of each model of iPhone you purchased during the applicable dates shown on the claim site, www.powerbuttonclassaction.com.
The takeaway: The deadline for filing a claim is March 23, 2020. The amount of the claim could be up to $24 per device, but there are no guarantees as payouts will come from the $20 million settlement and will be based on the number of claims. If you purchased one of the qualifying models during the specified timeline and suffered from a broken power button, you should file a claim even though the settlement amount is far less than the cost of a replacement phone.
Macy's data breach
Earlier this week Macy's reported they suffered a data breach on their website. In the breach, malicious scripts hacked their site and then stole customer's payment information. This type of attack is called MageCart, which consists of compromising a web site to inject malicious JavaScript into the site for the purpose of capturing payment information submitted by customers.
The Macy's site was hacked on October 7 and by October 15 Macy's had become aware of the situation and removed the malicious code. In this breach, attackers were able to gain access to the following customer information:
- First and last name
- Address including city, zip and state
- Phone number
- Email address
- Payment card number, security code, and expiration if submitted when checking out
All relevant credit card companies have been notified and Macy's has hired a third party to help with their investigation.
The takeaway: Data breaches are serious and can happen at any time. Always use caution when entering personal data, but know that sometimes nothing can be done on your part to protect yourself if using an infected site. If you are a victim of the Macy's breach, you should receive an email directly from Macy's. Also, it is important to always keep a close eye on your credit card statements to watch for fraudulent charges.
Bluetooth scanning to locate laptops and phones
An article from WIRED this week discusses how smash and grab car break-ins are likely far less random than once thought. Some thieves are now using Bluetooth scanning to find devices that respond using the Bluetooth beacon. This helps them locate cars with devices in them, effectively alerting them which cars are more profitable to break into.
Tech gadgets are always sought after items for theft. They are easy to turn over, bring in decent money, are used by virtually everyone and are often on our person. As thieves become more sophisticated, we need to be smarter to protect ourselves from theft.
The takeaway: The best thing you can do is never leave a device inside your car. In addition to theft, high temperatures are especially bad for devices. Additionally, losing the device to a smash and grab means you must also pay to fix your car which compounds the loss. If you must leave a device in your car, put it in a place that cannot be seen from the outside and most importantly, temporarily disable Bluetooth so the device cannot be located this way.
Technology changes quickly and it is nearly impossible to be aware of every new application, new feature, security flaw, data breach, Ransomware attack, and even physical attack against our devices. However, as shown in the examples above, the more you know, the more protected you will be. Knowing thieves are using Bluetooth scanning may save a device. Knowing about the Apple settlement may lessen a loss. Knowing about the Macy's data breach may prevent fraudulent charges.
As always, knowing how to protect yourself, your data, and your devices is the key!

