Security Updates: Infected Android Apps, Twitter Vulnerabilities and GPS Trackers
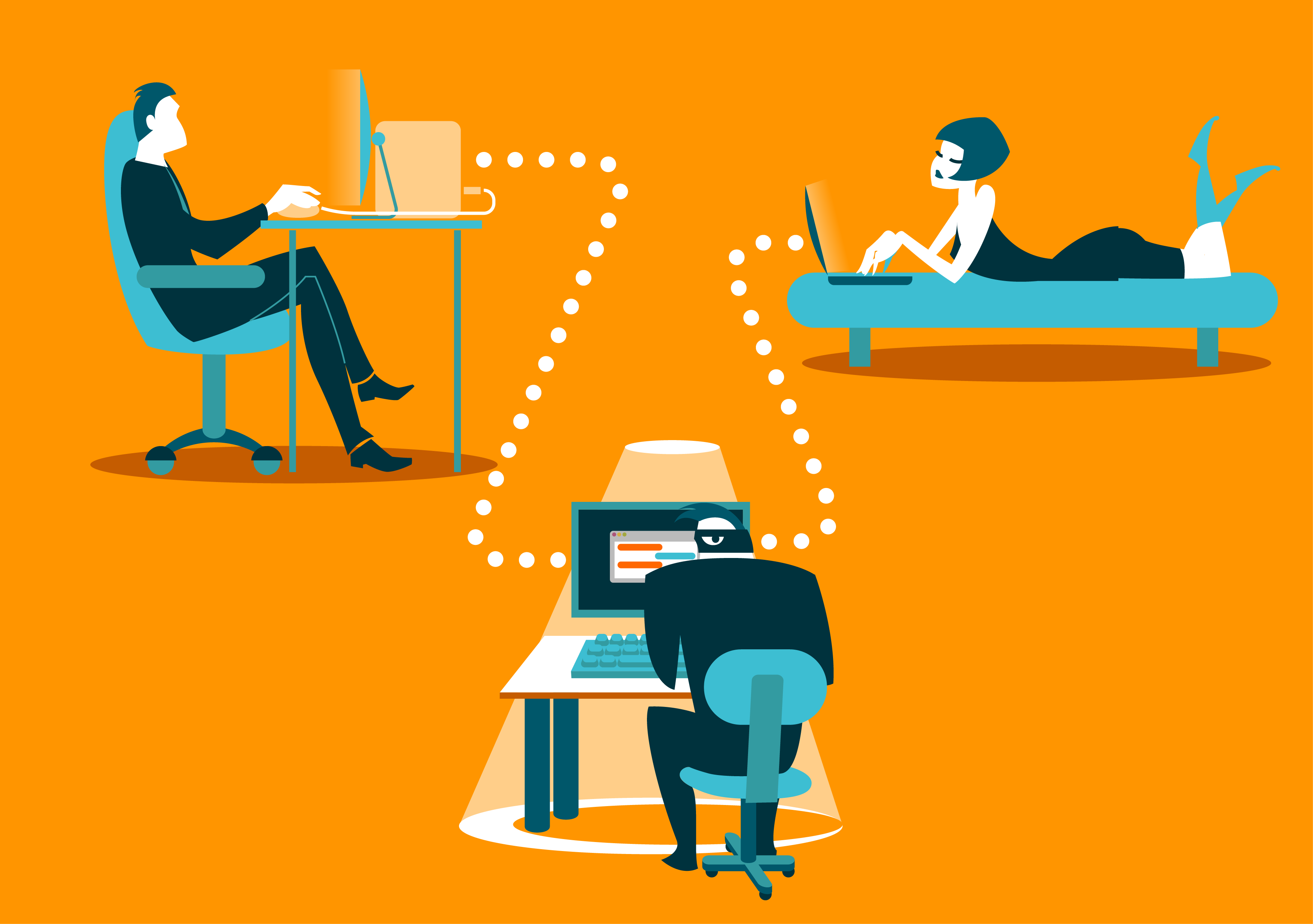
Each week there are more data vulnerabilities and attacks released into the wild, exposed by cybersecurity analysts and patched by app developers. The last few weeks have been no exception to this unfortunate reality. This post discusses several recent threats including infected Android apps removed from the Google Play store, apps leaking Twitter API keys, and a critical flaw in GPS trackers allowing them to be hacked.
Security Updates: Infected Android Apps, Twitter Vulnerabilities and GPS Trackers
The following recently exposed security threats are ones likely to affect most users so it is important to be aware they exist.
Infected Android apps
Google recently removed eight apps from the Play store, and while this might seem miniscule in the totality of apps available in an app store, these apps had over three million downloads before being pulled. The apps in question included a type of fleeceware, meaning the app unknowingly subscribes users to premium services. Additionally, fleeceware can access the user's SMS messages.
The eight apps in question are:
- Coco Camera v1.1 (com.toomore.cool.camera)
- Creative 3D Launcher (app.launder.creative3d)
- Freeglow Camera 1.0.0 (com.glow.camera.open)
- Funny Camera by KellyTech
- Gif Emoji Keyboard(com.gif.emoji.keyboard)
- Razer KeyboaRd & Theme by rxcheldiolola
- Vlog Star Video Editor (com.vlog.star.video.editor)
- Wow Beauty Camera (com.wowbeauty.camera)
What you need to know: If you installed any of these apps, be sure to remove them immediately. Then, run a scan on your smartphone for any other malicious apps. Lastly, verify you do not have any unrecognized subscriptions on your credit card. It is good practice to check your credit cards for rogue charges once a quarter even if something has not happened to trigger it.
For more information about this threat, read this article.
Twitter vulnerabilities
Recently a vulnerability uncovered more than 3,000 mobile apps exposing Twitter API keys. This vulnerability exposes the API keys to the public, meaning a hacker could take over the Twitter account that a user associated with the bad app. Most people are probably familiar with apps that ask for permissions to other apps when installed or when you try to use all the features. For example, plenty of apps ask for permission to your camera, microphone, etc.
Twitter, like many apps, allows integrations with other apps. When installed, these apps ask users to associate their Twitter account with it. Unfortunately, some of these apps were exposing the API keys that this process utilizes. This meant, when exploited, hackers could use those keys to log into Twitter, create and delete tweets, read and send messages, and more, all while using the victim's Twitter account.
What you need to know: It is always good practice to allow the least amount of permissions between applications. If you have a problem, it can be harder to figure out which app is causing the exposure, etc., when you have allowed dozens or hundreds of apps to associate with other accounts that include login credentials. If you begin to notice things on your Twitter account that you have not done, change your Twitter password immediately. You may also have to deny other apps access to it. Slowly re-associate only those apps you know and trust with your Twitter credentials to try and prevent this from happening again.
For more about this threat, read this article.
GPS trackers
The US government recently notified the public that they should stop using the Micodus MV720 GPS tracker after a critical vulnerability was found in the tracker's software. There are several vulnerabilities in the device, one of which allows man-in-the-middle attacks, which is where a hacker can capture all the data sent between two devices without the user's awareness. Because the device uses unencrypted HTTP to communicate, anyone who gains access to the traffic to and from the device will be able to read it in plain text.
Another vulnerability in this GPS tracker allows hackers to utilize a hardcoded key on the device to access it and monitor and control all communications with the device.
What you need to know: If you own one of these devices, which cost around $20, you are better off not using it until these security vulnerabilities have been patched. Since these GPS trackers are at such a low price point, you might be better off purchasing a more secure replacement.
For more about this vulnerability, read this article.
There will always be new threats, vulnerabilities, and attacks being propagated, taken advantage of, and exposed. While it may be impossible to steer clear of every single threat, what will greatly increase your odds of protecting devices and your private data is staying informed about the current types of attacks. Knowing what is going on, how the attacks are being carried out and how you can avoid them, will go a long way towards preventing you from being low hanging fruit, which is of course what hackers are looking for.
As always, making decisions when it comes to purchasing software and hardware, and providing credentials for one app in another app, should be done in an informed and cautious way!

