Security Round Up: Voicemail, COVID-19 & Consent-Based Phishing Attacks
As long as there are businesses and individuals with private information on devices that connect to the internet, scammers will actively try to gain unauthorized access to that information for nefarious purposes. The reasons why, the attack types and the way the information is used varies greatly. Sometimes it is used to make some quick money, other times taking over user's accounts or even to funnel thousands into the wrong accounts.
This week we discuss some current scams focusing on phishing attacks in the form of voicemail, app consent and of course, COVID-19.
Security Round Up: Voicemail, COVID-19 & Consent-Based Phishing Attacks
A phishing attack is a type of attack that appears to come from a reputable person, someone you would probably recognize, like a business associate or an officer in a business. These attacks typically use email to communicate with a potential victim. The purpose of course is to get you to share information, which hopefully leads to access you would otherwise not provide.
Phishing emails often include links that redirect you to an authentic looking site that is spoofed in hopes of getting you to enter your credentials. Other times emails will request money be wired to a specific account to pay a vendor for example, but the account is owned by the scammer. There are several other ways these attacks and scams work, but they boil down to the wrong person getting ahold of actual business information, client information or funds.
Voicemail phishing
The purpose of a recent voicemail phishing scheme is to steal the credentials used with enterprise applications. The scam operates by sending a html attachment in an email to potential victims. The attachment claims to be a link to a voicemail for that individual.
When clicked, users are prompted to enter their credentials to log in to hear the message. Unfortunately, the URL the link is directed to is not a legitimate company site. Next the user is prompted to enter their credentials into the spoofed company page created by the scammers. Once a user complies, the scammer has their credentials. Interestingly, this attack also incorporates Google's reCAPTCHA service which only further convinces users the page is legitimate.
The takeaway: Always use caution clicking links in emails. Anytime you follow a link in an email and are prompted to enter credentials or other private information, be very cautious! This goes for every type of attack past, present and future. Also, if someone really needs to get ahold of you, they will call back, email, text, or message you via social media. In other words, they will find a way to get ahold of you. Clicking links in email is easy, but clicking without thinking will eventually cost you far more than you think.
COVID-19 Phishing
Since the pandemic began, there have been and continue to be a vast array of scams relating to COVID-19. So much so that it does not make sense to address a single one here. Instead, I want to share some tips for staying knowledgeable about it and any future virus because it is important to know what is happening.
- One of the best things you can do to protect yourself is to go after the information directly, rather than getting sucked into click-bait news stories or spammy emails. This means going to a search engine and searching for news, or specific news items. When you finish an article, go back to the original search and find other stories from there. Try to avoid clicking from story to story to story as these articles are often ad-like and can be spam.
- If you are interested in getting daily updates or notification, subscribe to a reputable online news source. This way you are expecting their emails and can be fairly certain they are legitimate.
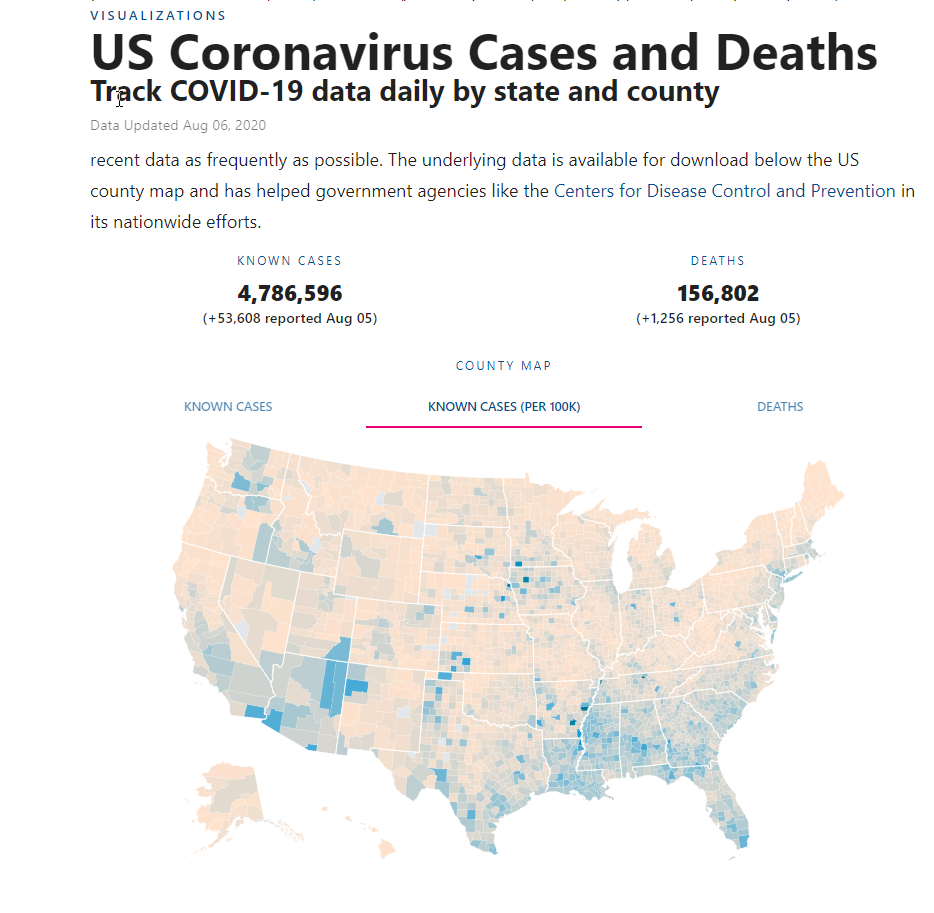
- Visit reputable sites that cover information about the virus. Many are free and include varying types of information about the status of each state. Some examples are USA facts which have information about every state and county as well as DATA USA which also has information about each state including confirmed cases and more.
- Sign up at state websites for alerts and regular information briefings. Also check with your mayor, local senators and congressman who often communicate on a far more regular basis, and whose information is more directly related to you.
The takeaway: Unfortunately, news stories about the virus are not going to slow down until after the virus is no longer a viable threat. Being informed is great, but staying away from click-bait articles which can be a security threat will help protect your devices and personal data.
Consent Phishing
Consent-based phishing attacks are a newer type of attack that prompts users to consent to permissions for apps. Unfortunately, a by-product of consistently being forced to allow apps access to certain features on smart phones means many people no longer consider what access they are giving. Being prompted to consent to access barely causes concern, which can cause problems.
Much of the time app access is warranted. For instance, if you want to accept Square payments you have to provide access to location services which is necessary to reduce fraud. Using the Zoom app requires access to the camera and microphone for more obvious reasons. While these are legitimate examples, with this latest threat, giving access to an app without knowing how it is being used might provide unauthorized access to your email, forwarding rules, contacts, notes, profile and more, according to Microsoft.
In this particular attack, potential victims are sent a link that when clicked, prompts them to provide consent to a malicious app that then allows scammers to access user's private data.
The takeaway: Once again this attack requires user interaction in the form of clicking a bad link and giving the malicious app consent to access items it should not have. Always use caution when giving consent to apps on your smartphone. Many times you will be prompted with multiple consents. Stop and take the time to look at each consent request and ask yourself why the app might need that access or what it could do with it. If you are not sure, deny the access. This can always be changed later if necessary.
With more and more people working from home, phishing scams have become more commonplace. People are more connected to their email, messaging platforms and video conferencing than ever. This makes email scams more viable and popular. Scammers will always do their best to make it easy to hack you. Be cautious opening unsolicited emails and especially clicking on links in emails and websites.
As always, the more careful you are the less likely you will be an easy target!

