Security Round Up: Google Doc and WordPress Vulnerabilities Plus Malicious USB Drives
Several new security vulnerabilities and threats have been exposed over the last few weeks. It is impossible to cover all of the threats, and many affect only a very small portion of the population. Here we cover more commonly used software and applications that are likely to affect greater numbers of people in hopes of helping them protect their privacy and data.
This post discusses three recent threats including a vulnerability in Google docs, security patches to WordPress, and USB drives with Ransomware being mailed to unsuspecting users.
Security Round Up: Google Doc and WordPress Vulnerabilities Plus Malicious USB Drives
Feel free to jump directly to a section:
Google docs
A vulnerability in Google docs was found last June, but in December a new wave of hackers began exploiting this security risk. The hack includes using comments on Google apps, including docs, to send users malicious links.
How it works: Hackers leave comments on a Google doc using the @ symbol and tagging the author, another user, or anyone they want to target. This automatically generates an email notification that is sent to the tagged user. What makes this so effective is that the email notification is sent from Google, a legitimate source that users expect to receive email from and often do not question opening. Unfortunately, these notifications include the original post and the malicious link which puts recipients at risk.
What you can do: As with any email or ads within websites, etc., it is important to be careful clicking on links. Keep in mind this includes clicking links sent from people you know as it is possible they were not the one sending it to you. Additionally, as in this case, a legitimate sender can still send malicious links and present a security risk.
WordPress
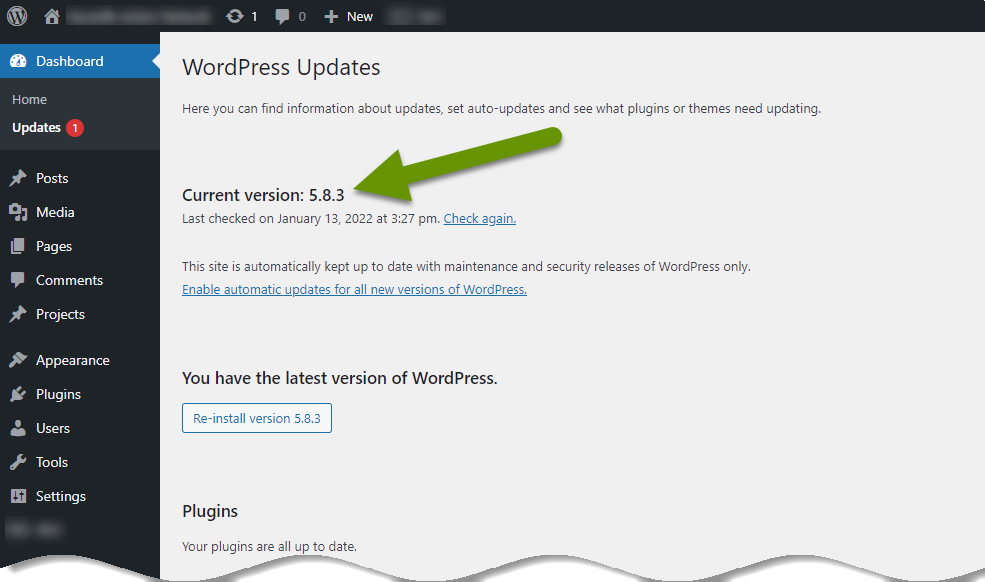
An updated version of WordPress, version 5.8.3, was recently released. This update includes fixes for four vulnerabilities. The issues addressed include two SQL injection vulnerabilities, a cross site scripting flaw and an object injection issue per WordPress's security release page. Three of these issues have been rated with high severity.
How these work: While these types of hacks fall beyond the scope of this post, it can be helpful to understand a little bit about how they work. For example, SQL injections are vulnerabilities where additional data is sent in a data field that breaks the logic on the backend. This allows an attacker to query data they normally would not have access to, and should not have access to. The information entered to break the logic is often masked in a user name or password because this is legitimate information that should be passed along. Unfortunately, in this case, it is used to extract data that should not be accessed.
What you can do: If you have a WordPress website, log into your Dashboard and verify the site has been updated to version 5.8.3. If not, create a backup of your site, if possible, then manually update the site. Also, it is always a good idea to regularly log in and ensure updates are being installed as well as installing updates for all active plugins and themes.
USB drives
USB drives have been being used to introduce viruses and other malware to unsuspecting individuals for years. From the time they became popular they have been used as a way to spread malware at conferences and trainings.
USB drives are often taken from areas where they are being handed out for free so malicious software can be added to them, then brought back as if they never left. This is how users pick them up without suspecting anything bad is on them. Other times USB drives are brought in and dumped in bowls or left with other available drives with malicious software pre-installed.
A recent attack using USB drives has been identified by the FBI as ransomware infected drives are being mailed to businesses working in the transportation and insurance industries. This targeted attack began back in August of 2021.
How it works: Hackers impersonate legitimate companies like Amazon, Health and Human Services, or others, to convince users to connect the external USB drive to their device. Based on who they are impersonating, hackers may promise users counterfeit gift cards, that the drives contain COVID-19 guidelines, or anything else they think will convince a user to connect the USB drive to their device.
Once a user connects the USB drive to their device the hackers have won. The device is recognized as a trusted keyboard and proceeds to infect the system through a series of steps. The end goal is to get onto the network and install Ransomware on critical system devices.
What you can do: Refrain from connecting any USB drives you are not familiar with or that do not belong to you, into your devices. Be especially cautious of devices sent to you or that you did not initiate getting. Most companies no longer include cd's with the software or drivers for their products. Instead, they typically include a link to their website where the most recent version of the software can be downloaded and installed. This is the best way to get this information.
There will always be newly introduced security threats to our data and privacy. The best thing we can do to protect against threats like those introduced with Google docs, WordPress vulnerabilities and ransomware infected USB drives, is to be careful what we interact with and keep our systems up-to-date at all times. Lastly, never let someone push you into taking action without thinking it through as this is often when people get tricked.
As always, taking the time to slow a conversation down can save you far more time later!

