One New Reason Ransomware Victims Should NOT Pay - US Sanctions
Suffering a ransomware attack is something every business owner hopes to avoid. Nobody wants to lose access to their own data, data they have potentially spent years developing, managing and building. Unfortunately, this is exactly what happens when you are successfully hit with ransomware because the files are encrypted.
Successful offsite backups are the best protection against a ransomware attack. In the absence of backups, businesses often feel forced to pay the ransom, which only encourages more attacks.
This post discusses a new reason why ransomware victims should not pay.
One New Reason Ransomware Victims Should NOT Pay - US Sanctions
Just this week a coordinated ransomware attack hit dozens of hospitals located in California, New York and Oregon. However, ransomware is a huge threat to businesses of all sizes and industries. Part of what makes ransomware so dangerous is the way it operates. Not only does ransomware encrypt all the files on your local device, but it also encrypts the following:
- Files on locally attached storage drives including USB flash drives, SD cards, etc.
- Files on other computers or servers on the same network that the infected computer has access to.
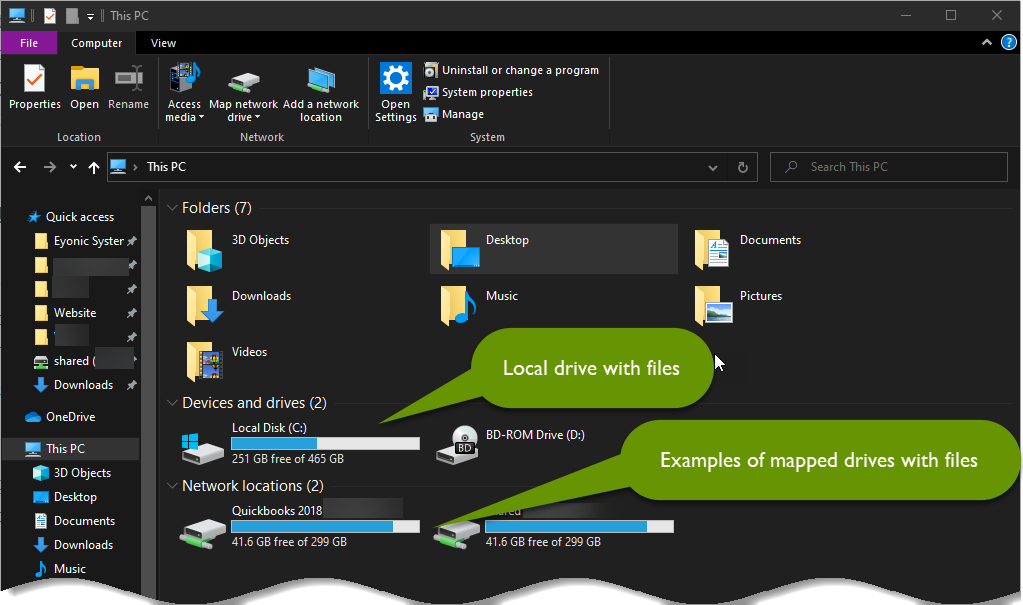
In essence, ransomware encrypts all the local files in addition to files accessible via a mapped drive. Mapped drives are used to connect a device with files located on another device. There are many reasons to use mapped drives, including, but not limited to:
- Connecting someone to files where you can only have a single copy of the file, such as a database like QuickBooks, etc.
- Centrally managing files for the purposes of backups, etc.
- Controlling file versions so that everyone is always using the latest and greatest version of each file.
- Making files accessible to multiple users at once, such as from a server, that is always available to users.
- Efficiently sharing files between a couple of computers on a home network, rather than needing to attach files to emails or copy to flash drives, etc.
Since mapped drives are so useful, they are often used by individuals as well as businesses. Unfortunately, sharing access to files using mapped drives to provide employees what they need to carry out their job functions, puts those files at risk. All it takes is for one device to become infected to encrypt all of the business data. This is why frequent offsite backups are the only real protection from a ransomware attack.
Another problem with ransomware is that even if you pay the ransom, you might not receive the decryption key. Remember, you are dealing with thieves who have stolen your ability to access your data. They might send you the correct decryption key, but they also might not. Even if they do, there is nothing to stop them from hitting you again.
The new rule that affects ransomware victims in the US
As of earlier this month, there is an even bigger reason not to pay the ransom caused by a ransomware attack. If you are a business or individual in the United States making a ransom payment to a group that is under economic sanctions, you could incur sanctions for paying the group. This change comes from the US Treasury Department's Office of Foreign Assets Control.
Companies that fall victim to a ransomware attack and any third-party companies that help facilitate the recovery process for those businesses, need to be aware of these sanctions as both can be held responsible.
NOTE: You could be sanctioned and held responsible for paying the ransom to a group under economic sanctions EVEN IF you were unaware you were doing so.
The ransomware process is severe, and is often devastating to a business. At the very least, it is costly, even if a ransom is not paid. Once an attack is successful, the business loses access to critical business data. From there it spreads and infects the network wherever possible. All devices should be taken offline to protect them. Infected devices should be rebuilt from scratch before being allowed back on the network.
Once a machine has been rebuilt, it will need to have all necessary programs and applications reinstalled. Finally, files can be restored to the device. This of course assumes you have access to a recent copy of those files. Once the data is restored, your business can finally begin to get back to normal.
Unfortunately, if you are missing any of these pieces along the way - licensing, software installers, copies of your data, someone who can manage these operations on your behalf - you are more likely to feel forced to pay the ransomware. Complicating this further is the fact that you could also suffer sanctions if paying the ransom.
The takeaway: Paying the ransom is never the best route to take after a ransomware attack. One of the biggest reasons is ransom payments further encourage hackers to continue to use these types of attacks against companies. It is every business owner's responsibility to do everything they can to keep from paying a ransom, in hopes that someday these attacks will become less effective and not worth the effort to pursue.
If you do not have an offsite or cloud-based backup solution in place, make this your utmost priority right now! Cloud-based backups are preferred as they should be located offsite, have file versioning, and be available 24/7. Whatever you do, be sure you check and make sure the right files are being backed up, that you can access them, that they can be restored properly, and most importantly, that they are being backed up regularly!
Falling victim to a ransomware attack is something every business hopes to avoid. Unfortunately, attacks can come at any time and often hit multiple targets at once as in the recent attack against hospitals in the US. The recovery process from a ransomware attack typically spans several days to weeks, which is costly to your business. These attacks can also damage the reputation of your business. Knowing that your business might also be responsible for sanctions if you pay the ransom, it is more important than ever to invest in backups, thereby avoiding the need to pay a ransom.
As always, being proactive will save you time and money, and in this case, possible sanctions!

