It's Consumer Protection Week - Here's 4 Ways to be Safer Online
This week is National Consumer Protection week and as while there are many threats to our user data and personal information, there are also a multitude of ways we can protect ourselves. Some examples of best practices are:
- Using a credit card rather than debit card - this prevents you from needing to enter a pin in public where people can visually capture your input.
- Using Apple or Google Pay - these applications store your credit card so you do not need to physically access the card to use it.
- Using a unique PIN for debit cards - not reusing this pin for unlocking cell phones or as voicemail codes, etc.
- Never sharing passwords, account access, and credit or debit cards with others.
There are other, more advanced threats to the security of your devices. It is important to be aware of them as this increases your ability to protect yourself from them.
It's Consumer Protection Week - Here's 4 Ways to be Safer Online
There are far more than four approaches to staying safe in an online environment, but these ideas can be implemented immediately. Most importantly, remember to slow down when you are feeling pressured. Hackers often use scare tactics to appeal to your emotional, and less rational, feelings to get you to act without thinking. If you stop and think about what is going on before reacting, you will be less likely to make a big mistake.
Reduce the amount you rely upon search
Search became the answer for all our woes years ago. Can't remember where you stored a file? Forgot the name of the file or when it was created? Can't figure out where a setting went? Not to worry, search to the rescue! The problem with using search this way is that it allows us to pay less attention to what we are doing. We rely upon, or anticipate using search later, which makes us lazier as we are confident search will provide what we need.
Where this can hurt us is relying upon search to find company websites. It would be challenging to find someone who has never experienced clicking on a website result only to find it was not what we were looking for. This is not a big deal when searching for a specific item not tied to a company. However, for banking and other websites that would need to collect personal information, this is much riskier. If you imagine the drive home from work and how easy it can be to forget part of the trip, this is what can happen when we use search all the time - we forget to stop and consider what we are clicking.
The fix: Bookmark the correct site instead of searching and absently clicking on results.
Don't click or call the number in popup warnings
Popup warnings are different from ads and website interactions like subscribing to a newsletter or signing up for a coupon. By contrast, these are the warnings claiming your computer has been infected and you need to call (enter the company here) so they can fix your computer. Oftentimes they pretend to be Microsoft or other reputable companies to encourage people to call. Unfortunately, these popups use shady scare tactics to convince people to let them connect remotely when you otherwise would not.
What is important to know is that getting a popup that you have been infected does not guarantee you have been infected. In other words, a popup can claim anything but it does not make it true. People who call are encouraged to allow the company to connect remotely so they can "clean their computer". At this point typically one of two things happens. The user either overpays for software to remove malware from their computer that likely never existed in the first place, or worse case, this is when the real malware is installed.
The fix: Close the web browser. If the popup returns, reset the browser to factory settings or if necessary, uninstall the browser and reinstall it.
Most importantly, do not ever let someone remotely connect to your computer unless you know who they are and trust them. Remote control software was created for a great purpose - to allow technicians to help people without physically being in the same location. It can also be used to run updates and install software when users are not actively on their computers, as is the most common case with businesses. Unfortunately, those settings that make it great for remote tech support also make it dangerous when misused.
Look for more than the lock symbol next to a website

This is important because we have all been taught to look for the lock symbol next to a website to be confident the site is encrypting our data before transferring it. Unfortunately, it is not enough for a website to have this symbol. The symbol means a security certificate has been purchased for the domain. However, it does not mean it is a trustworthy website or that it is safe to enter your information.
As an example, Wells Fargo's website is wellsfargo.com. If you were unknowingly redirected to wellsfargo.online.com and someone made this fake site look just like Wells Fargo's website, you might be tricked into entering your credentials. In situations like this, the lock symbol does not protect you because you are submitting your information directly to the hackers. While the lock does show the site is secure, if you are using the wrong site, your information is still at risk.
The fix: Always be sure to check the URL before entering your credentials. This is especially important when using search or clicking on links in email, which I recommend doing cautiously. It is easy to be redirected without realizing it. Check the URL in its entirety provides the greatest likelihood you will never fall for this trick.
Go directly to a site rather than clicking on a link in an email
Last but not least, clicking on links in emails can be very risky. There are examples of emails with safe links including, but not limited to:
- Newsletters you have subscribed to and trust
- Emails received after clicking a link on a website to reset a password or recover an account
- Deals or product information emails from companies you trust and that you actively signed up to receive
Aside from emails you are expecting or have consented to receive, use caution clicking on links. This is especially true of threatening emails or emails using scare tactics like you need to change your password because there was a data breach, etc. Keep in mind, a link's text can be anything and the destination link might not match the text.
A hyperlink contains two parts: the text describing the link and the actual link destination. The text may look like this: "Check out our sale now!" and appear to have come from a company you subscribe to, but the hyperlink could be pointing to a nefarious website hoping to gather your personal data.
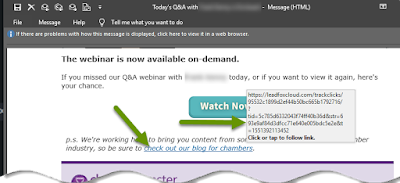
The fix: Hover over the link to see where the link is really going. Instead of using the link, go to the site directly or call the company to see if there really is a problem with your account. The more we notify companies of scams like this, the better they can inform other customers and the safer we will all be.
During the National Consumer Protection Week, and every week, it is important to do your best to protect yourself. Going directly to websites rather than using search, checking to make sure you are at the correct website before entering your credentials, refusing to click on ads using scare tactics and using caution with links in emails are ways you can protect yourself from common attacks schemes happening all the time.
As always, knowing what form an attack may take will better help you identify the risks so you can avoid them rather than becoming a victim!

