3 Ways to Protect Devices Now that you Work From Home
The best way to protect devices from malicious attacks, including Ransomware, is to be alert. Unfortunately, there is no real way to prevent attacks, only preventing them from being successful. Using caution, staying informed, and making decisions at your own pace, rather than responding to external pressures, is the best way to prevent attacks from being successful.
Most employees are not aware of all the protections their employers have in place. Obviously this protects their client data, but they can also protect you as well. Now that so much of the workforce is working from home, it is likely you do not have the same protections in place that you did when you went to an office. Some protections are installed on your local device, like endpoint protection, while others operate at the network level. Protections operating at the network level can include:
- Intrusion detection systems, known as IDS.
- Intrusion prevention systems, known as IPS.
- Firewalls, which help prevent unauthorized access to devices from outside the business, can stop certain suspect executables from running, and much more.
This post discusses three ways to protect your devices as you now work from home and likely have less protections in place.
3 Ways to Protect Devices Now that you Work From Home
Attacks on users have continued during the pandemic. What has changed is the level of protections users have. Below are three areas of concern that should be considered by everyone who is working from home.

Ransomware
Ransomware is a malicious attack that encrypts all of the files on an infected device. Once infected, the user can no longer open any of the files on that device. Additionally, it spreads and encrypts files on locally attached USB drives, as well as mapped drives.
This means if you access files on a server via a mapped drive, even if you are only connected to that server using a VPN because you are not in the same physical location, those files will also be encrypted. This is one of the main reasons why Ransomware is so dangerous.
Once a user's device is encrypted by Ransomware, they are prompted to pay a ransom in bitcoin to obtain the decryption key. Unfortunately, there is no guarantee you will receive the key, that the key will work, or that you will not be attacked again.
What you can do to protect yourself: The only true protection from Ransomware is the ability to recover from an attack. This means having offsite, cloud-based backups. These backups need to be reliable, as well as performed regularly. Having backups from a month ago is better than nothing, but not really that helpful for most businesses considering how much data they deal with daily.
It is always important to be careful clicking links on websites, in emails, and downloading applications you are not familiar with, to help prevent an infection in the first place.
Email introduces the potential for all kinds of attacks. If you think about it, every business uses email, most every employee has email, and people can't simply stop using it because it is a vital part of business and personal communication. From an attacker's perspective, this makes it a viable way to try and manipulate employees so they can gain unauthorized access to business or personal information.
Some of the biggest threats are focused in a few categories:
- Collecting payments - there are several different types of scams related to garnering payments. Some focus their attacks on people in the C-Suite, hoping to get them to click on a link in a phishing email. Once they gain access they can begin spreading all kinds of misinformation like sending instructions to the Finance department for wire transfers that route back to the hacker's accounts. Other times emails are sent outside of the company to the victim's contacts, again asking for payments to be made to the hacker's accounts.
- Access to company information - for almost any company, your client list is one of your biggest assets. This includes the names, addresses, and purchasing patterns of your clients which hackers often sell for a profit. Also of high importance is any proprietary data or intellectual property.
- Ransomware - any company that instantly, and unsuspectingly, loses access to its data is going to be in a world of hurt. This is what makes a Ransomware attack so effective. Without reliable, and most importantly recent data backups, a company can be unable to resume operations without paying the ransom. This is why it is absolutely critical to make sure your business has daily, offsite/cloud-based backups and that they are checked regularly for data consistency.

What you can do to protect yourself: First, if you are questioning the validity of an email, there is probably a reason. You should always err on the side of caution and delete anything you even remotely think might be a scam. If you do this, the worst that can happen is someone has to send the email again, or contact you another way. Doing this is much less likely to cause you extended grief or downtime, while trying to recover from malware surely will.
Second, if you do work in the finance department, always call someone who "sent" you an unusual payment request before following through on it. At the very least, create a new email and ask them if they sent the payment request. Do not reply to the original email.
Lastly, be careful clicking on links in emails, even from users or companies you know or do business with. There is no telling when they themselves might suffer from an attack or have their email spoofed.
Firewalls
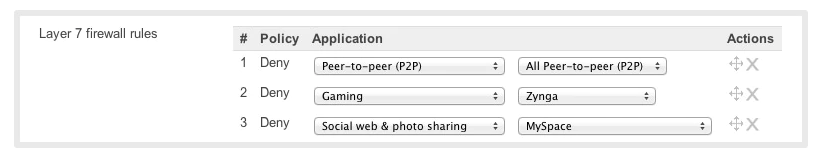
Most businesses, especially larger ones or those that are involved with people's personally identifiable information (PII) have firewalls onsite. Firewalls serve many purposes including:
- Protecting devices from incoming attacks and breaches using IPS and IDS.
- Preventing users from downloading software that is suspected of being malicious. This is typically prevented when a user visits a website and tries to run an installer, but can also be blocked when files are sent in emails, etc.
- Maintaining the confidentiality, integrity and availability of company and user data by preventing unauthorized access to the internal network.
- Prioritizing and blocking certain types of traffic.
Working from home, most users have modems provided by their internet service provider (ISP) that sits at the edge of their network. At a business, the modem is connected to the firewall which then filters down to switches and end user devices. At your home, most people connect directly to their modem or connect to it wirelessly, without other protections in between. Many modems have some built-in protections, but these are never as robust as a separate firewall.
What you can do to protect yourself: Because purchasing a separate firewall can be expensive (some of which require continued licensing to receive updates), it does not make sense for everyone to invest in these devices. Instead, be careful when downloading software, make sure it is coming from a reputable location. If you are unsure, contact your employer's IT staff as they can provide guidance and often-times links to download that are known to be safe.
Don't let other people use the device you use for your business, especially not logged in as you. If you have to share a device, be sure to create a secondary user account with limited permissions. Also, never share your passwords with anyone and try not to reuse important passwords.
The ability to work from home might be the difference between working or not working, while we slog through this pandemic. In the future, more companies may choose to employ a greater portion of staff who work at home. If you are working from home, you need to consider some of the areas external threats pose a greater threat: Ransomware, email, and firewalls. In each case, using caution is one of the most important things you can do to protect yourself. The information above will greatly increase your ability to maintain your data privacy and integrity.
As always, external threats will continue, but caution, preparation and staying informed, reduces the odds of suffering an attack.

