2 Current Scams you Need to be Aware of: Zoom Phishing & HIPAA
It is unfortunate, but new scams are regularly introduced into the online ecosystem. Some scams piggyback off of older ones or use pieces of existing malware to launch while others are completely new. The one constant is that the more common a business or service, the higher the likelihood hackers will focus an attack on that business or its clients.
Consider the following categories and examples:
- EMail - GMail, Comcast, AT&T, Mac mail, Yahoo
- Online shopping accounts - Amazon, Walmart, Target
- Banking - Wells Fargo, Chase, Bank of America
- Organizations/Government - IRS, HUD, CDC, EDD, DMV
These are examples of larger organizations, companies and services that most people are familiar with. This makes them a larger target for a hacker because of the size of their audience. By using common, widely-used companies, hackers have a bigger target which increases the number of victims they will have.
2 Current Scams you Need to be Aware of: Zoom Phishing & HIPAA
With so many threats to our privacy and data, it is important to be diligent about emails, calls and even physical mail that claims to be from 'customer support'. Physical mail threats are far less common, but are still worth our attention. This is especially true for communications asking you to reset passwords, provide personal information and other similar data.
Below are two current scams: the first is a company now being widely used for business and educational communications and the other focuses on privacy requirements that affect many business categories.
Zoom meeting phishing attacks
The recent meteoric rise of the video conferencing service Zoom, has left it the target of all kinds of security attacks. Some were fairly harmless - people dropping into meetings they were not invited to because the link was posted publicly. Others were inappropriate - uninvited people showing up without clothing. Still others were such a nuisance - loud music, etc. - that the meetings had to be shut down.
After these issues were reported, Zoom stopped all programming for new features and focused solely on beefing up its security measures and rolling out updates to prevent further issues. However, a new scam has come about that attacks the video conferencing service from a completely different angle.
The scam uses phishing emails with Zoom meeting links. Many of these emails are coming from users whose emails have been hijacked. Others are sending users to domains that are not actually linked to Zoom. Some examples of these domains are zoomvideoconference.com and zoomcommunications.com. Once someone clicks the bad link they are directed to a fake login page in hopes of capturing their user credentials for services like Office 365.
If hackers get these credentials they can use them to get into your email. From there they can send emails on your behalf, send infected emails to all of your contacts, send payment requests to clients, change passwords to other accounts you have, add email rules, and much more!
The Takeaway: This is another example where it is extremely important to verify the sender of the email, not just look at the "From" name the creator of the account used. Remember, the name that appears in the "From" field can be set to anything regardless of whether it relates to the email account or not.
For instance, I can create a new email like newuser45921@gmail.com and set the display name to be Eyonic Systems so people think the email is coming from my business. Naming the email after my business does not mean the email is from a legitimate @eyonic.com account. This is why only looking at the "From" field of an email can be misleading and potentially dangerous.
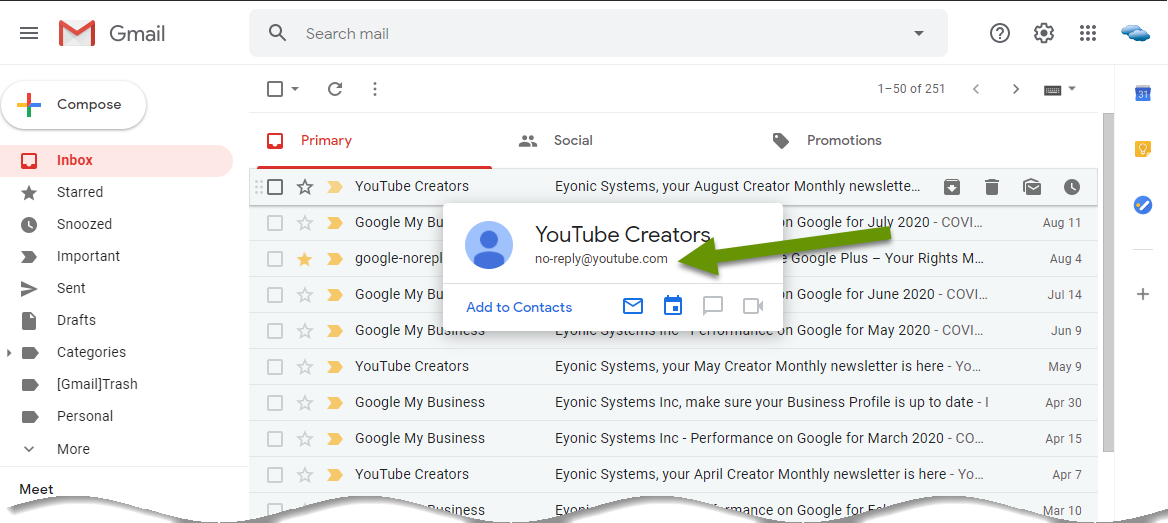
Luckily, many webmail applications provide a popup of the actual sender when you hover over any email. In the example below you can see that the email claiming to be from "YouTube Creators" is in fact from a @youtube.com email address.
In some situations it is best to delete an email without even opening it, such as when:
- The email is from a company you do not do business with.
- The email uses scare tacticts like having subject lines saying "RESET YOUR PASSWORD BEFORE BEING LOCKED OUT OF YOUR ACCOUNT" or "You are the subject of an audit", etc.
- The emails are unsolicited, meaning you did not engage with the company in any way, or sign up for emails from them.
HIPAA Compliance postcards
HIPAA compliance is required for businesses that have or store personally identifiable information (PII) on their customers. The most common examples of these types of companies are medical and dental offices, physicians and doctor groups, and chiropractors. Each of these groups typically have a great deal of private information about their clients as they would not be able to provide sufficient care without that information. Unfortunately, that kind of information is highly sought after.
A recent warning from the Department of Health and Human Services (HHS) Office for Civil Rights (OCR) shared information about a scam utilizing a postcard claiming to come from "HIPAA Compliance Officers". Like many other attacks, this one uses fear to try to get people to act without thinking. There is even a couple of sentences describing the potential monetary penalties for violations!
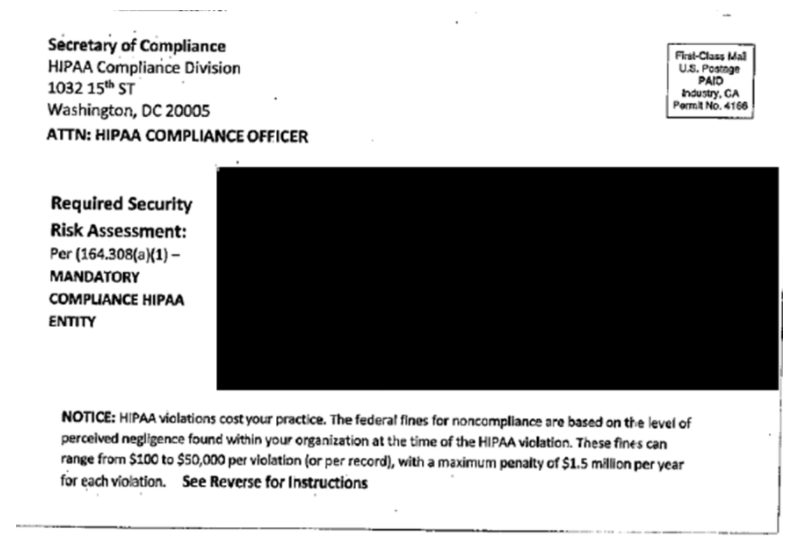
While the postcard claims to be from an entity that does not exist, any business required to meet HIPAA compliance rules would take a security audit seriously. The purpose of the postcard is to push people to reach out so the senders can get people signed up for a costly service. This service is with a private company and is not from HHS or OCR. It is also important to note that OCR HIPAA audits are announced to the public in advance and do not use scare tactics like this postcard.
The takeaway: The postal service is rarely used in scams like this because mail fraud is a serious crime. However, that does not mean it is never done, so it is important to question something that does not seem right no matter how it comes to you. Once again, any communications - regardless of type - using scare tactics is most likely a scam.
Follow up by finding legitimate contact information for the supposed sender, call or email the company they claim to be and find out if the information is real. Do not use any contact numbers, weblinks or emails sent in the communication. The small amount of time it takes to find the real contact information will be worth not being hacked.
The more common a company or service, the more likely they and their customers will be targeted by people trying to steal user credentials and data. This is an unfortunate truth, but there are ways you can protect yourself. Use caution clicking on links in emails, always avoid taking action when a communication uses scare tactics, and delete unsolicited emails.
As always, slowing down and using caution will save you far more time in the long run!

